As we approach 2025, the importance of robust cybersecurity measures cannot be overstated. With cyber threats evolving at a rapid pace, both individuals and organizations must stay ahead of the curve to protect their digital assets.

The demand for skilled cybersecurity professionals is on the rise, with jobs expected to grow by 32 percent between 2022 and 2032. Implementing effective security practices, such as using password managers, enabling Two-Factor Authentication (2FA), and utilizing Virtual Private Networks (VPNs), is crucial for safeguarding against phishing, ransomware, and other cyber threats.
Key Takeaways
- Stay informed about the latest cybersecurity threats and trends.
- Implement robust password management and 2FA.
- Use VPNs for secure internet browsing.
- Regularly update software and systems.
- Invest in cybersecurity certifications for professionals.

The Evolving Cybersecurity Landscape in2025
The evolving cybersecurity landscape in 2025 demands a proactive approach to digital security. As technology advances, cyberattacks are becoming more frequent and sophisticated, making robust protection essential for both individuals and organizations.
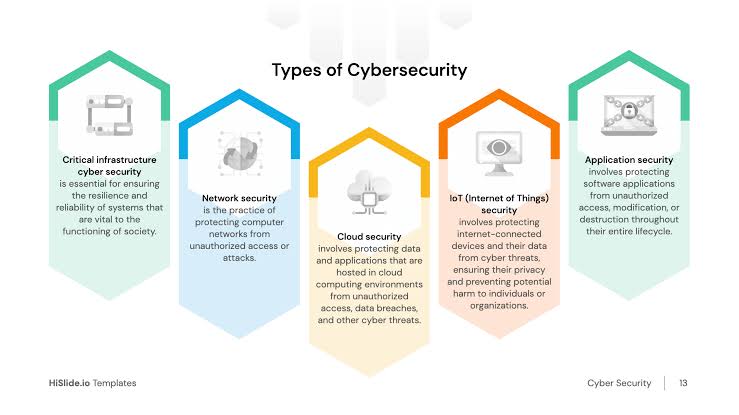
Key Trends Shaping Digital Security
Several key trends are shaping the digital security landscape in 2025. Artificial Intelligence (AI) and Machine Learning (ML) are being increasingly used to enhance cybersecurity measures. These technologies help in predicting and mitigating threats more effectively.
- AI-powered threat detection systems
- ML-driven incident response frameworks
- Enhanced encryption methods
Another significant trend is the adoption of Zero Trust Architecture, which operates on the principle of verifying every access request as though it originates from an open network.
The Expanding Digital Attack Surface
The digital attack surface is expanding due to the proliferation of IoT devices, cloud services, and remote work environments. This expansion creates new vulnerabilities that attackers can exploit.

| Attack Vector | Description | Mitigation Strategy |
|---|---|---|
| Phishing Attacks | Social engineering tactics to steal sensitive information | Employee training, email filtering solutions |
| Ransomware | Malware that encrypts data, demanding ransom for decryption | Regular backups, endpoint protection |
In conclusion, the cybersecurity landscape in 2025 is characterized by evolving threats and the need for advanced security measures. By understanding key trends and expanding attack surfaces, organizations can better prepare against potential threats.
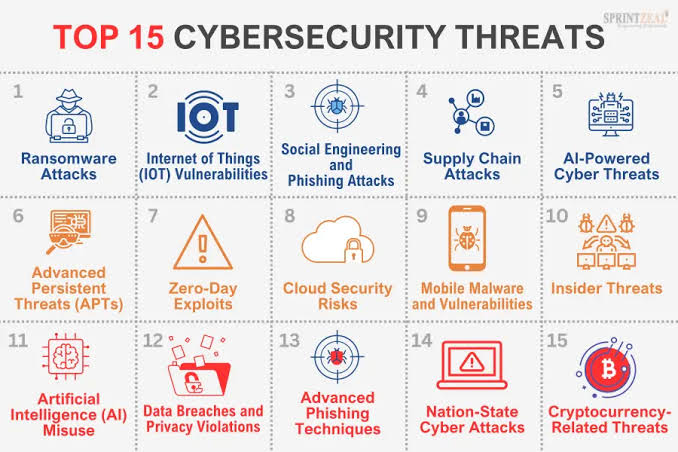
Understanding the2025 Threat Landscape
As we approach 2025, the cybersecurity threat landscape continues to evolve at an unprecedented rate. The increasing reliance on digital technologies has expanded the attack surface, making it easier for cybercriminals to exploit vulnerabilities.
Common Attack Vectors and Vulnerabilities
Cyber attackers are leveraging various tactics to breach security systems. Phishing and ransomware attacks remain prevalent, with attackers using sophisticated social engineering techniques to deceive victims. The rise of remote work has also introduced new vulnerabilities, particularly in endpoint security.
A detailed analysis of common attack vectors reveals the following trends:
| Attack Vector | Description | Impact |
|---|---|---|
| Phishing | Social engineering attacks via email or messaging apps | Data theft, financial loss |
| Ransomware | Malware that encrypts data, demanding ransom for decryption | Data loss, financial loss, operational disruption |
| Zero-day Exploits | Attacks on previously unknown vulnerabilities | Unexpected data breaches, system compromise |
Emerging Threats from AI and Quantum Computing
The advent of AI and quantum computing is introducing new cybersecurity challenges. AI-powered attacks can automate and enhance the sophistication of cyberattacks, making them harder to detect. Quantum computing, on the other hand, poses a threat to current encryption methods, potentially rendering them obsolete.
To stay ahead of these emerging threats, organizations must adopt proactive cybersecurity measures, including investing in AI-powered security solutions and quantum-resistant cryptography.
Personal Cybersecurity Essentials for2025
As technology advances in 2025, individuals must be proactive in protecting their online presence. With the rise of digital threats, personal cybersecurity has become a critical concern.
Password Management and Authentication
Effective password management is the first line of defense against cyber threats. Using a password manager can significantly enhance security.
Top Password Managers in 2025
Some of the top password managers in 2025 include LastPass, 1Password, and Dashlane. These services offer robust encryption and user-friendly interfaces.
Two-Factor Authentication (2FA) Best Practices
Implementing 2FA adds an extra layer of security. Best practices include using authenticator apps like Google Authenticator or Authy, and avoiding SMS-based 2FA when possible.
Secure Browsing and Communication
Secure browsing and communication are crucial in protecting personal data. Utilizing the right tools can make a significant difference.
Virtual Private Networks (VPNs) for Personal Use
VPNs encrypt internet traffic, providing a secure connection. Popular VPN services include ExpressVPN and NordVPN.

For secure communication, using encrypted messaging apps like Signal or WhatsApp is recommended. These platforms ensure that conversations remain private.
By adopting these personal cybersecurity essentials, individuals can significantly reduce their risk of falling victim to cyber threats in 2025.
Enterprise Cybersecurity Best Practices for2025
With cyber threats becoming more sophisticated, enterprises must adopt advanced cybersecurity measures to safeguard their digital assets in 2025. As the digital landscape continues to evolve, it’s crucial for organizations to stay ahead of potential threats by implementing robust security protocols.
Zero Trust Architecture Implementation
One of the key strategies in enhancing enterprise cybersecurity is the implementation of a Zero Trust Architecture. This approach operates on the principle of “never trust, always verify,” ensuring that every user and device is authenticated and authorized before accessing network resources. By adopting a Zero Trust model, enterprises can significantly reduce the risk of data breaches and cyber attacks.
Network Segmentation Strategies
Another critical aspect of enterprise cybersecurity is network segmentation. By dividing the network into smaller, isolated segments, organizations can limit the spread of malware and unauthorized access. This strategy not only enhances security but also simplifies the process of monitoring and managing network traffic.
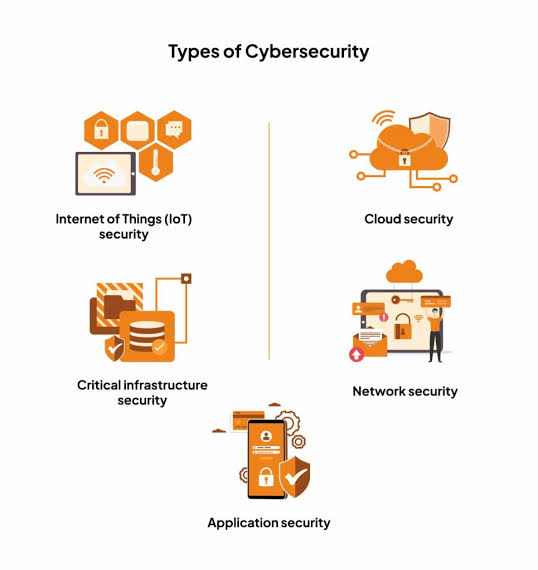
Cloud Security Frameworks
As more enterprises move their operations to the cloud, implementing robust cloud security frameworks is becoming increasingly important. These frameworks provide a structured approach to managing cloud security risks, ensuring compliance with regulatory requirements, and protecting sensitive data. By leveraging cloud security frameworks, enterprises can confidently adopt cloud services while maintaining a strong security posture.
In conclusion, adopting enterprise cybersecurity best practices in 2025 involves a combination of Zero Trust Architecture, network segmentation, and robust cloud security frameworks. By implementing these strategies, organizations can significantly enhance their cybersecurity posture and protect against the evolving threat landscape.
Endpoint Protection: Securing Every Device
As the digital landscape expands, endpoint protection becomes increasingly crucial for safeguarding devices and data. With the rise of remote work and the proliferation of connected devices, securing every endpoint is vital to protecting against cyber threats.
Mobile Device Security Solutions
Mobile devices are a significant vulnerability point in many organizations. Implementing robust mobile device security solutions is essential. This includes using mobile device management (MDM) software, enforcing strong passwords, and ensuring regular software updates.
IoT Device Protection Strategies
The Internet of Things (IoT) has introduced a myriad of security challenges. IoT device protection strategies involve segmenting IoT devices on separate networks, using strong passwords, and regularly updating firmware. It’s also crucial to monitor IoT devices for suspicious activity.

Remote Workforce Endpoint Security
With the shift to remote work, securing remote workforces has become a priority. This involves implementing endpoint detection and response (EDR) tools, using virtual private networks (VPNs), and conducting regular security awareness training.
| Endpoint Type | Security Measures | Benefits |
|---|---|---|
| Mobile Devices | MDM software, strong passwords, regular updates | Enhanced security, reduced risk of data breaches |
| IoT Devices | Network segmentation, strong passwords, firmware updates | Reduced vulnerability to cyber attacks |
| Remote Workstations | EDR tools, VPNs, security awareness training | Improved security posture, reduced risk of cyber threats |

In conclusion, endpoint protection is a multifaceted approach that requires attention to various device types and use cases. By implementing robust security measures for mobile devices, IoT devices, and remote workstations, organizations can significantly enhance their overall security posture.
The Critical Differences: Personal vs. Organizational Cybersecurity Risks
As we navigate the complex cybersecurity landscape of 2025, it’s crucial to understand the distinct risks faced by individuals and organizations. While both personal and organizational cybersecurity are vital, the nature of threats, vulnerabilities, and protective measures differ significantly between these two domains.
Individual Vulnerability Points
Individuals face unique cybersecurity challenges, primarily through personal devices and online behaviors. Common vulnerability points include weak passwords, susceptibility to phishing attacks, and the use of unsecured public Wi-Fi networks. To mitigate these risks, individuals should implement strong password management practices, enable two-factor authentication, and remain cautious when interacting with emails and websites.

Organizational Attack Surfaces
Organizations, on the other hand, have broader and more complex attack surfaces. These include not only employee endpoints but also servers, cloud services, and third-party integrations. Organizational risks are heightened by factors such as insider threats, sophisticated phishing campaigns targeting employees, and vulnerabilities in software and hardware. To combat these threats, organizations must adopt comprehensive security strategies, including network segmentation, regular security audits, and employee cybersecurity training.

Tailoring Security Approaches to Different Contexts
Understanding the differences between personal and organizational cybersecurity risks is key to developing effective security measures. For individuals, this means adopting best practices for personal device security and online safety. For organizations, it involves implementing robust, multi-layered security frameworks that address the unique challenges of their IT environments. By tailoring security approaches to their specific contexts, both individuals and organizations can better protect themselves against the evolving threats of 2025.
Phishing Attacks in2025: Sophisticated Tactics and Defenses
Phishing attacks have become increasingly sophisticated in 2025, leveraging advanced social engineering techniques to deceive victims. These attacks are not only more complex but also more targeted, making them harder to detect.
Current Phishing Statistics and Trends
The latest statistics on phishing attacks reveal a concerning trend. According to recent reports, phishing attempts have increased by over 30% in the past year, with a significant portion targeting financial institutions and healthcare organizations.
| Industry | Phishing Attempts | Success Rate |
|---|---|---|
| Finance | 250,000 | 12% |
| Healthcare | 180,000 | 9% |
| Technology | 150,000 | 7% |
Advanced Social Engineering Techniques
Attackers are now using advanced social engineering techniques, including AI-generated emails that closely mimic legitimate communications. These emails often create a sense of urgency, prompting victims to reveal sensitive information.
Common tactics include:
- Using personalized information to build trust
- Creating fake login pages that appear legitimate
- Employing psychological manipulation to create a sense of urgency
Email Spoofing and Credential Theft Prevention
To prevent email spoofing and credential theft, organizations are implementing advanced email security solutions, including DMARC, SPF, and DKIM protocols. These measures help verify the authenticity of emails and reduce the risk of phishing attacks.

By staying informed about the latest phishing tactics and implementing robust security measures, individuals and organizations can significantly reduce their risk of falling victim to these sophisticated attacks.
Ransomware Evolution: New Threats and Protection Strategies
Ransomware evolution is a pressing concern in 2025, driven by advancements in Ransomware-as-a-Service (RaaS) and double extortion tactics. As cyber threats become more sophisticated, it’s crucial for individuals and organizations to understand the changing ransomware landscape and implement effective protection strategies.
Ransomware-as-a-Service (RaaS) Developments
RaaS has democratized ransomware attacks, making it easier for less skilled attackers to launch sophisticated campaigns. This development has led to an increase in ransomware attacks, as the barrier to entry is significantly lowered. RaaS platforms provide a comprehensive toolkit, including malware, payment processing, and customer support, making it a one-stop-shop for cybercriminals.

Double Extortion and Data Exfiltration Tactics
Double extortion tactics have become more prevalent, where attackers not only encrypt data but also exfiltrate sensitive information, threatening to release it publicly unless a ransom is paid. This dual-threat approach increases the pressure on victims to comply, making it a highly effective strategy for cybercriminals.
Effective Ransomware Defense Frameworks
To combat the evolving ransomware threat, implementing a robust defense framework is essential. This includes:
- Regular backups and disaster recovery plans
- Advanced threat detection and response systems
- Employee education and awareness training
- Network segmentation and access controls
By adopting these strategies, individuals and organizations can significantly reduce their vulnerability to ransomware attacks and protect their critical data.
Cybersecurity Trends2025: Personal Cybersecurity Tips and Enterprise Cybersecurity Innovations
As we dive into 2025, the cybersecurity landscape is rapidly evolving with innovative trends that promise to revolutionize both personal and enterprise security. The integration of advanced technologies like AI, automation, and quantum-resistant protocols is set to redefine how we approach cybersecurity.
AI-Powered Personal Security Solutions
AI-powered personal security solutions are becoming increasingly sophisticated, offering enhanced protection against complex cyber threats. These solutions leverage machine learning algorithms to detect and respond to potential security breaches in real-time.
- Advanced Threat Detection: AI systems can analyze vast amounts of data to identify patterns and anomalies that may indicate a cyber threat.
- Personalized Security: AI-driven security solutions can tailor their protection based on individual user behavior, providing a more personalized security experience.
Enterprise-Grade Automated Defense Systems
Enterprise-grade automated defense systems are crucial for organizations to stay ahead of sophisticated cyber threats. These systems utilize AI and machine learning to automate threat detection and response.
- Rapid Incident Response: Automated defense systems can respond to security incidents in real-time, minimizing potential damage.
- Scalability: These systems can scale to meet the needs of large organizations, providing comprehensive security across complex networks.
Quantum-Resistant Security Protocols
With the advent of quantum computing, traditional encryption methods are at risk of being compromised. Quantum-resistant security protocols are being developed to address this challenge.
- Post-Quantum Cryptography: Implementing cryptographic algorithms that are resistant to quantum attacks is a key focus area.
- Hybrid Solutions: Some organizations are adopting hybrid solutions that combine classical and quantum-resistant cryptography to ensure long-term security.
In conclusion, the cybersecurity trends of 2025 are centered around leveraging AI, automation, and quantum-resistant technologies to enhance both personal and enterprise security. By adopting these innovations, individuals and organizations can stay ahead of emerging threats and protect their digital assets effectively.
Threat Intelligence: Building a Proactive Security Posture
In the ever-changing world of cybersecurity, threat intelligence platforms are emerging as a key component of proactive security strategies. As cyber threats become more sophisticated, organizations are turning to threat intelligence to anticipate and mitigate potential attacks.
Leading Threat Intelligence Platforms
Several threat intelligence platforms have gained prominence for their capabilities in enhancing cybersecurity. These platforms provide critical insights into emerging threats, helping organizations bolster their defenses.
IBM QRadar Capabilities
IBM QRadar is a comprehensive threat intelligence platform that offers advanced security analytics and incident response capabilities. Its ability to integrate with various data sources makes it a powerful tool for identifying and mitigating threats.
ThreatConnect Integration Features
ThreatConnect is known for its robust integration features, allowing seamless connectivity with existing security infrastructure. This enables organizations to leverage threat intelligence across their security operations.
CrowdStrike Falcon Intelligence provides real-time threat intelligence, helping organizations stay ahead of adversaries. Its focus on proactive defense strategies makes it a valuable asset in the cybersecurity arsenal.
Recorded Future Analytics
Recorded Future offers advanced analytics capabilities, providing insights into the threat landscape. Its ability to analyze vast amounts of data helps organizations identify potential threats before they materialize.
Implementing Effective Monitoring Systems
Effective threat intelligence is not just about having the right tools; it’s also about implementing effective monitoring systems. This involves continuous surveillance of the threat landscape and rapid response to emerging threats.
By integrating threat intelligence platforms with monitoring systems, organizations can enhance their proactive security posture, ensuring they are always prepared to face potential cyber threats.
Essential Cybersecurity Tools for2025
The year 2025 demands robust cybersecurity measures, with several key tools emerging as essential for digital safety. As threats become more sophisticated, organizations and individuals must leverage advanced technologies to protect their digital assets.
Next-Generation Firewalls
Next-generation firewalls (NGFWs) have become a critical component of cybersecurity infrastructure. They offer advanced threat detection and prevention capabilities beyond traditional firewalls.
Palo Alto Networks Solutions
Palo Alto Networks provides comprehensive NGFW solutions that include advanced threat prevention, URL filtering, and application control. Their solutions are designed to protect against known and unknown threats.
Fortinet FortiGate Capabilities
Fortinet’s FortiGate NGFWs offer a range of capabilities, including high-performance threat inspection, SSL inspection, and network segmentation. These features help organizations secure their networks against sophisticated attacks.
Endpoint Protection Platforms
Endpoint protection platforms (EPPs) are crucial for safeguarding endpoints from various threats. Modern EPPs incorporate AI and machine learning to enhance threat detection and response.
CrowdStrike Falcon Protection
CrowdStrike’s Falcon platform provides real-time endpoint detection and response, leveraging AI to identify and mitigate threats. It offers comprehensive visibility across endpoints, enabling swift incident response.
SentinelOne Autonomous Security
SentinelOne’s autonomous security platform uses AI to detect, prevent, and respond to threats in real-time. It provides a unified solution for endpoint protection, detection, and response.
Email Security Solutions
Email remains a significant attack vector for cyber threats. Advanced email security solutions are essential for protecting against phishing, malware, and other email-borne threats.
Proofpoint Advanced Threat Protection
Proofpoint’s Advanced Threat Protection (ATP) uses a combination of techniques, including sandboxing and threat intelligence, to detect and block advanced threats delivered via email.
Mimecast Email Security
Mimecast’s email security solutions provide comprehensive protection against email threats, including spam, malware, and targeted attacks. They also offer email continuity and data leak prevention.
| Tool Category | Solution | Key Features |
|---|---|---|
| Next-Generation Firewalls | Palo Alto Networks | Advanced threat prevention, URL filtering |
| Endpoint Protection | CrowdStrike Falcon | Real-time detection and response, AI-driven |
| Email Security | Proofpoint ATP | Sandboxing, threat intelligence |
Security Operations Centers (SOCs): Integration and Optimization
With the rise of sophisticated cyber threats, the integration and optimization of SOCs have become paramount. Security Operations Centers are critical in detecting, responding to, and preventing cyber threats. Their effectiveness, however, depends on how well they are integrated and optimized.
Modern SOC Architecture and Components
A modern SOC is built on a foundation of advanced technologies and skilled personnel. It comprises various components, including threat intelligence platforms, security information and event management (SIEM) systems, and incident response tools. These components work together to provide comprehensive security.
Tool Integration for Comprehensive Security
Tool integration is vital for a SOC’s effectiveness. By integrating various security tools, SOCs can gain a more comprehensive view of their security posture. This integration enables better detection and response to threats. For instance, integrating threat intelligence feeds with SIEM systems can enhance threat detection capabilities.
Automation and Orchestration in SOCs
Automation and orchestration are key to optimizing SOC operations. They enable SOCs to respond quickly and effectively to security incidents. Automation helps in reducing manual tasks, while orchestration ensures that different security tools work together seamlessly.
| Component | Function | Benefit |
|---|---|---|
| Threat Intelligence Platforms | Provides insights into emerging threats | Enhances threat detection |
| SIEM Systems | Monitors and analyzes security event logs | Improves incident response |
| Incident Response Tools | Facilitates response to security incidents | Reduces response time |
Incident Response Planning for2025
In the ever-evolving cybersecurity landscape of 2025, incident response planning stands out as a critical component of organizational resilience. As cyber threats become more sophisticated, having a well-structured incident response plan is essential for minimizing the impact of security breaches.
Building Effective Response Frameworks
A robust incident response framework is the backbone of any effective cybersecurity strategy. It involves identifying potential threats, outlining response procedures, and establishing clear communication channels. “A well-planned incident response strategy can significantly reduce the financial and reputational impact of a cyberattack,” as emphasized by cybersecurity experts.
Tabletop Exercises and Simulations
Tabletop exercises and simulations are vital for testing the efficacy of an incident response plan. These exercises allow teams to practice their response to various scenarios, identify weaknesses, and improve their coordination. Regular simulations help ensure that the response team is prepared for real-world incidents.
Post-Incident Analysis and Improvement
After an incident, conducting a thorough post-incident analysis is crucial. This involves reviewing the response efforts, identifying areas for improvement, and updating the incident response plan accordingly. Continuous improvement is key to staying ahead of emerging threats.
By focusing on these aspects, organizations can develop a comprehensive incident response plan that not only mitigates the impact of cyber incidents but also enhances their overall cybersecurity posture.
In-Demand Cybersecurity Certifications for2025
As we approach 2025, the cybersecurity landscape continues to evolve, making certifications more crucial than ever. Cybersecurity professionals must stay ahead of emerging threats by acquiring relevant certifications that validate their skills and knowledge.
Advanced Security Certifications
Advanced security certifications are designed for experienced professionals looking to demonstrate their expertise in cybersecurity management and leadership.
CISSP (Certified Information Systems Security Professional)
The CISSP certification is highly regarded in the industry, covering a broad range of security topics, including security management, asset security, and software development security.
CISM (Certified Information Security Manager)
The CISM certification focuses on information security management, making it ideal for professionals who manage, design, and oversee an enterprise’s information security.
Technical Security Certifications
Technical security certifications are essential for professionals who want to demonstrate their hands-on skills in cybersecurity.
CEH (Certified Ethical Hacker)
The CEH certification is designed for professionals who want to understand the mindset and techniques of hackers, enabling them to better protect their organizations.
Security+
Security+ is a widely recognized certification that covers a broad range of security topics, making it a great starting point for those new to cybersecurity.
CISA (Certified Information Systems Auditor)
The CISA certification is ideal for professionals who audit, control, and provide assurance over an organization’s information systems.
| Certification | Description | Target Audience |
|---|---|---|
| CISSP | Security management and leadership | Experienced security professionals |
| CISM | Information security management | Security managers and leaders |
| CEH | Ethical hacking techniques | Security professionals interested in penetration testing |
| Security+ | Broad security topics | Entry-level security professionals |
| CISA | Information systems auditing | Auditors and assurance professionals |
Career Advancement Through Certification
Obtaining relevant cybersecurity certifications can significantly enhance career prospects. Employers often prioritize candidates with certifications, as they demonstrate a level of expertise and commitment to the field.
Conclusion: Building a Resilient Cybersecurity Posture for2025 and Beyond
As we navigate the complexities of cybersecurity in 2025, it’s clear that building a resilient cybersecurity posture is crucial for both individuals and organizations. This requires a continuous effort to stay ahead of emerging threats, leveraging advanced tools and certifications to protect against ever-evolving cyber risks.
A robust cybersecurity posture involves implementing effective security measures, such as zero-trust architecture, endpoint protection, and threat intelligence. By staying informed about the latest cybersecurity trends and best practices, individuals and organizations can better safeguard their digital assets.
The future of cybersecurity demands adaptability, vigilance, and a proactive approach. By prioritizing resilient cybersecurity, we can mitigate potential threats and ensure a safer digital landscape for all.
FAQ
What are the most significant cybersecurity threats in 2025?
The most significant cybersecurity threats in 2025 include phishing attacks, ransomware, and emerging threats from AI and quantum computing. Organizations and individuals must be aware of these threats to protect themselves.
How can I protect myself against cyber attacks in 2025?
To protect yourself against cyber attacks in 2025, use a combination of password management, 2FA, and VPNs. Additionally, stay informed about the latest cybersecurity trends and best practices.
What is the importance of threat intelligence in cybersecurity?
Threat intelligence is crucial in building a proactive security posture. It helps organizations stay ahead of emerging threats and vulnerabilities, enabling them to respond effectively to potential security incidents.
What are the best cybersecurity certifications for 2025?
Some of the most in-demand cybersecurity certifications for 2025 include CISSP, CISM, and CISA. These certifications can help advance your career in cybersecurity and demonstrate your expertise.
How does AI improve cybersecurity?
AI improves cybersecurity by enabling organizations to detect and respond to security incidents more effectively. AI-powered security solutions can analyze vast amounts of data, identify patterns, and predict potential threats.
What is zero trust security, and is it the future of cybersecurity?
Zero trust security is a security model that assumes that all users and devices are potentially malicious. It requires continuous verification and monitoring to ensure that only authorized users and devices have access to sensitive data. Zero trust security is gaining popularity and is considered a promising approach to cybersecurity.
How can organizations protect against ransomware attacks?
Organizations can protect against ransomware attacks by implementing effective defense frameworks, including regular backups, patch management, and employee education. They should also consider using ransomware detection and response tools.
What are the benefits of using a VPN for personal cybersecurity?
Using a VPN can help protect your personal data by encrypting your internet traffic and masking your IP address. This can help prevent cyber attackers from intercepting your data and tracking your online activities.
How can I stay up-to-date with the latest cybersecurity trends and threats?
You can stay up-to-date with the latest cybersecurity trends and threats by following reputable cybersecurity sources, attending industry conferences, and participating in online forums and communities.
What is the role of Security Operations Centers (SOCs) in cybersecurity?
SOCs play a critical role in cybersecurity by providing a centralized platform for monitoring, detecting, and responding to security incidents. They help organizations respond quickly and effectively to potential security threats.
What is quantum hacking, and how can it impact cybersecurity?
Quantum hacking refers to the potential for quantum computers to break certain encryption algorithms, compromising the security of sensitive data. Organizations must be aware of this emerging threat and consider implementing quantum-resistant security protocols.